Architecture
The perimeter-first system model behind FuZe.AI, routing, and observable execution.
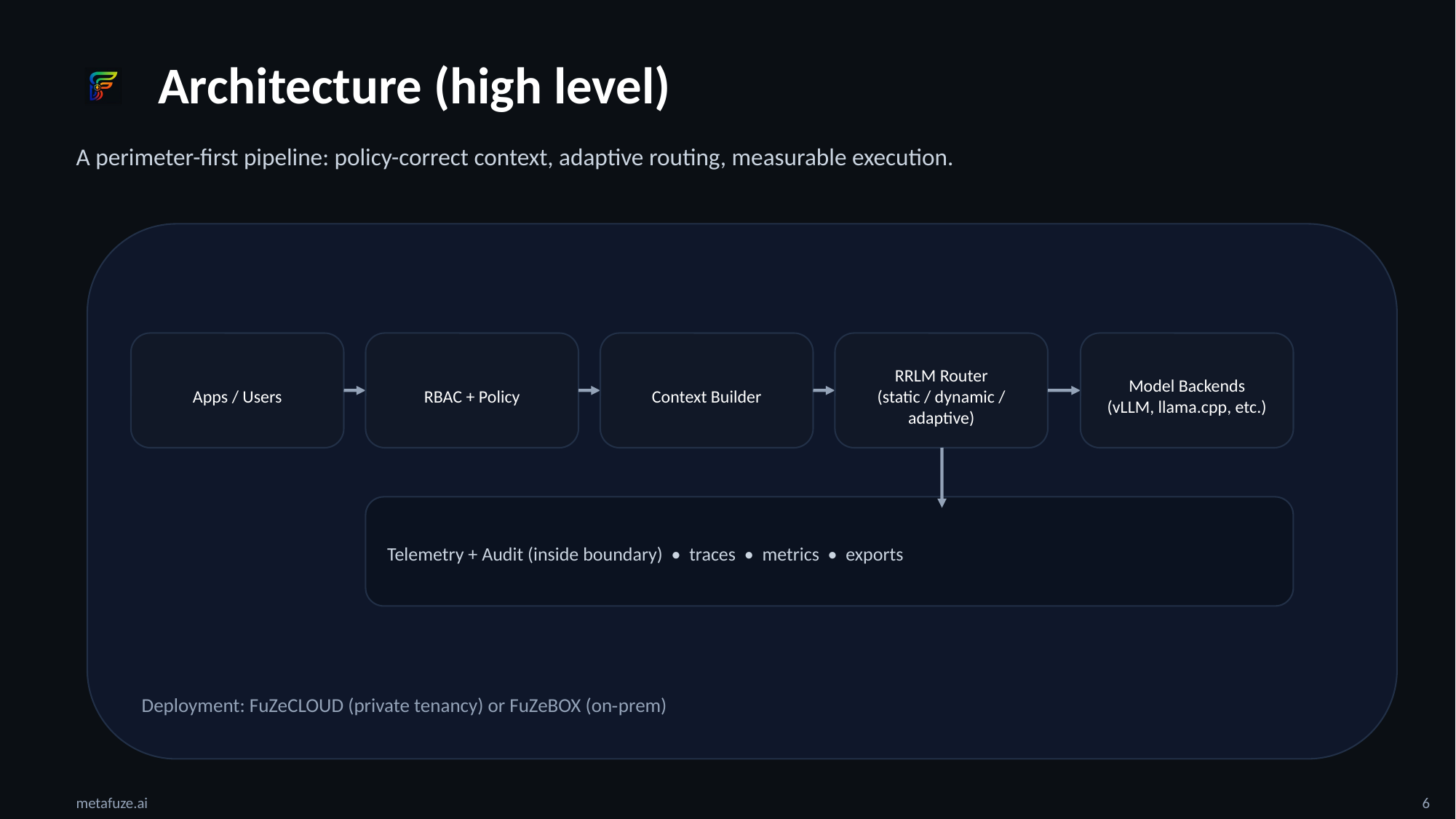
MetaFuZe is built around a simple idea: private AI should run inside your perimeter with controllable behavior, traceability, and production discipline. The control layer includes adaptive RRLM routing (Q-learning policy) and RBAC-aware context assembly. This diagram is intentionally high-level so it can map to both FuZeCLOUD (single-tenant) and FuZeBOX (on-prem).
Perimeter and tenancy
Designed to run inside your trust boundary. Choose single-tenant cloud or on-prem appliance deployment. Keep models, personas, telemetry, and audit trails private by default.
Adaptive routing (RRLM)
Route requests with control. Use static mode for strict determinism or dynamic mode for policy-based decisions. In adaptive mode, a Q-learning policy can learn a compact routing strategy from reward signals spanning quality, latency, and cost.
RBAC-aware context
Context assembly ties into role-based access control. Retrieval and memory are policy-correct per user and role, reducing leakage risk by design and keeping sensitive data out of context for unauthorized sessions.
Operational discipline
Benchmarks, readiness gates, and traceability hooks so AI behaves like an engineered system. Validate changes with repeatable tests, safe rollout patterns, and incident learning loops, not guesswork.
